Safeguarding the future: Tackling endpoint security in the post-Covid reality
Share:
Date:
July 2020

key fact
70% of breaches are perpetrated by external actors targeting end users, and attacks on Web apps accessed from endpoints play a role in 43% of incidents.
Previously in our Post-Covid Reality series, we examined the complexities of retrospectively auditing, optimising, and governing end user devices and technology. Across these operations lies the need to ensure that endpoints are properly secured to guard against multiple threats – especially as home working becomes more prevalent. So, what are the key issues to consider? Here, we look at:
- Why the cybersecurity landscape is more business-critical than ever before.
- The multi-faceted challenge of addressing physical, virtual, and cultural security threats.
- The importance of aligning operations and leadership to future-proof against cyber risk.
As reported in Forbes, securing endpoints will be the future of cybersecurity as we move to a post-pandemic culture of remote working. Q1 and Q2 2020 saw companies clamour to digitalise and virtualise their operations. But, in the process, security strategies have taken a back seat. This is unsurprising, given that companies have responded to Covid by prioritising the most immediate driver – ensuring continued productivity during lockdown.
However, 2020’s much anticipated Data Breach Investigations Report from Verizon makes for sobering reading. 86% of modern breaches are financially motivated, the data says, and 55% of breaches originate from organized crime groups. 70% of breaches are perpetrated by external actors targeting end users, and attacks on Web apps accessed from endpoints play a role in 43% of incidents. From an IT perspective, that makes the end user a key player in the security landscape.
What’s more, this is a multi-dimensional scenario. IT is tasked with mitigating not just reputational and operational risk, but the worrying financial threat that is becoming more aggressive. Cybercrime is notorious for its ability to stay one step ahead, and the rapid rollout of physical and virtual homeworking kit to millions of employees only renders the threat more urgent.
Navigating New Virtual Security Territory
The good news, as those on top of their IT strategy will know, is that the safeguarding toolkit is also evolving. In fact, according to the same Verizon report, only 24% of Cloud-based assets were involved in security breaches this year, versus 70% of on-premise infrastructures. Trust in Cloud-based systems has been growing for a long time now. But there remain companies who have dragged their heels, making them potentially more vulnerable. They have been forced by Covid to incorporate Cloud technologies into their digital suite in double quick time – perhaps without the capacity to properly address legacy issues at a time when speed of delivery is king and governance, may be bypassed altogether.
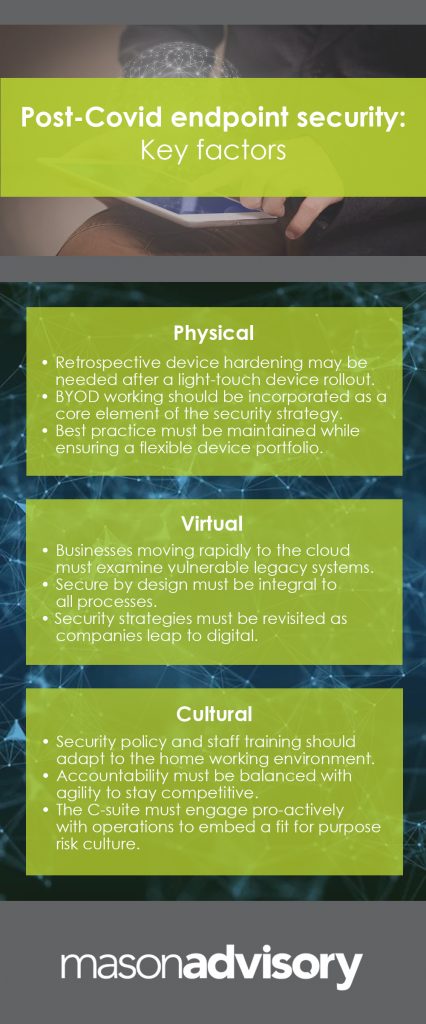
Those issues cross the areas of physical, virtual, and cultural management, because Covid 19 hasn’t just presented us with a rapid response scenario. It has driven new expectations of flexible working, introducing more complexity for IT at all levels. At the core of the matter lies device asset management – especially in a scenario where build and hardening may have been put to one side in favour of direct factory rollout. On the operational side, connectivity and SecOps processes must be addressed to ensure that safeguards are, at worst, retrospectively addressed and, at best, systemically architected into the strategy. The legislation landscape – especially in terms of data – is complex, presenting a challenging environment for multinationals getting to grips with shifting parameters in different locations.
The Human Factor in Post-Covid Cybersecurity
Added to all this, an accelerated uptake of video conferencing and virtual collaboration introduces new complexities to the area of governing behaviour. All the pen testing, authentication, encryption, patching and data security in the world won’t protect you if your people are not equipped to play their part. It’s fairly common knowledge that 90% of data breaches are caused by human error – but this goes way beyond data itself. Mix in the risks associated with BYOD, zero touch deployment, virtual connectivity, and multiple device usage. Then add the fact that half of employees have admitted to cutting cybersecurity corners when working from home during the pandemic. This is serious stuff, and it’s not going to go away.
So, whose head is on the block when endpoint security is on the agenda? The reality is that this needs to be a cross-operational effort. The CIO or CISO is responsible for understanding the real level of risk exposure. To do so, they should work in close synergy with all stakeholders, looking up, down and across the organisation and the external environment. Leadership must support operational functions in embedding not just the processes and tools, but the cultural understanding, policies and behaviours that will protect the business. Ultimately, this escalates all the way to the CEO, who faces the tricky task of balancing accountability and agility as we move further into remote and distributed working. Tools to safeguard systems and data without hindering productivity are becoming more sophisticated all the time. Ultimately, though, it’s the strategic mindset that lies at the heart of solving this particular post-Covid pain point.
Further insights
Read more articles on The Post-Covid Reality
Get inspired with our industry insights and case studies.
Make an enquiry with Mason Advisory
Author: Jagjeet Pandha
Published: LinkedIn